- (Topic 3)
While working in a coffee shop, an attacker watches a user log in to a corporate system and writes down the user's log-in credentials. Which of the following social engineering attacks is this an example of?
Correct Answer:
A
Shoulder surfing is the social engineering attack where an attacker watches a user log in to a corporate system and writes down the user’s log-in credentials. Social engineering is a type of attack that exploits human psychology and behavior to manipulate or trick people into revealing sensitive information or performing malicious actions. Shoulder surfing is a form of social engineering that involves observing or eavesdropping on someone’s screen, keyboard, or paper documents to obtain confidential information such as passwords, PINs, or credit card numbers. Shoulder surfing can be done in person or remotely using cameras or other devices. Shoulder surfing can be prevented by using privacy filters, locking screens, shielding keyboards, or being aware of one’s surroundings. References: [CompTIA Network+ Certification Exam Objectives], What Is Shoulder Surfing? | Definition & Examples | Forcepoint
- (Topic 3)
A network technician crimped a length of IJTP with TIAElA-568A on one end and TINE-IA- 5688 on the other. Which of the following cable types did the technician create?
Correct Answer:
A
The cable type that the technician created is a crossover cable. A crossover cable is a type of twisted-pair cable that has the transmit and receive pairs reversed on one end. A crossover cable is used to connect two devices of the same type, such as two switches or two computers, without using a hub or a switch. A crossover cable can be made by crimping one end of the cable with TIA/EIA-568A standard and the other end with TIA/EIA- 568B standard, or vice versa. These standards define the color coding and pin
assignments for RJ-45 connectors on twisted-pair cables. References: CompTIA Network+ N10-008 Certification Study Guide, page 53; The Official CompTIA Network+ Student Guide (Exam N10-008), page 2-4.
- (Topic 3)
A company ranis out a largo event space and includes wireless internet access for each tenant. Tenants reserve a two-hour window from the company each week, which includes a tenant-specific SSID However, all users share the company's network hardware.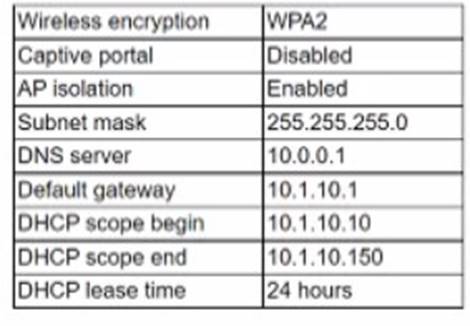
The network support team is receiving complaints from tenants that some users are unable to connect to the wireless network Upon investigation, the support teams discovers a pattern indicating that after a tenant with a particularly large attendance ends its sessions, tenants throughout the day are unable to connect.
The following settings are common lo all network configurations:
Which of the following actions would MOST likely reduce this Issue? (Select TWO).
Correct Answer:
DG
- (Topic 3)
While using a secure conference call connection over a corporate VPN, a user moves from a cellular connection to a hotel wireless network. Although the wireless connection and the VPN show a connected status, no network connectivity is present. Which of the following is the most likely cause of this issue?
Correct Answer:
C
A captive portal is a web page that is displayed to newly connected users of a Wi-Fi network before they are granted broader access to network resources. Captive portals are commonly used to present a landing or log-in page which may require authentication, payment, acceptance of an end-user license agreement, acceptable use policy, survey completion, or other valid credentials that both the host and user agree to adhere by123
A possible cause of the issue is that the user has not completed the captive portal authentication process, which prevents the VPN from establishing a secure connection over the Wi-Fi network. The user may need to open a web browser and follow the instructions on the captive portal page to gain full access to the internet.
- (Topic 1)
A user tries to ping 192.168.1.100 from the command prompt on the 192.168.2.101 network but gets the following response: U.U.U.U. Which of the following needs to be configured for these networks to reach each other?
Correct Answer:
B
A default gateway is a device that routes traffic from one network to another network, such as the Internet. A default gateway is usually configured on each host device to specify the IP address of the router that connects the host’s network to other networks. In this case, the user’s device and the destination device are on different networks (192.168.1.0/24 and 192.168.2.0/24), so the user needs to configure a default gateway on their device to reach the destination device. References: https://partners.comptia.org/docs/default-source/resources/comptia-network-n10-008-exam-objectives-(2-0), https://www.techopedia.com/definition/25761/default-gateway

