- (Exam Topic 2)
What is a capability of Cisco ASA Netflow?
Correct Answer:
A
https://www.cisco.com/c/en/us/td/docs/security/wsa/wsa11-0/user_guide/b_WSA_UserGuide/b_WSA_UserGui Policy Order The order in which policies are listed in a policy table determines the priority with which they are applied to Web requests. Web requests are checked against policies beginning at the top of the table and ending at the first policy matched. Any policies below that point in the table are not processed. If no user-defined policy is matched against a Web request, then the global policy for that policy type is applied. Global policies are always positioned last in Policy tables and cannot be re-ordered.
- (Exam Topic 1)
In which form of attack is alternate encoding, such as hexadecimal representation, most often observed?
Correct Answer:
C
Cross site scripting (also known as XSS) occurs when a web application gathers malicious data from a user. The data is usually gathered in the form of a hyperlink which contains malicious content within it. The user will most likely click on this link from another website, instant message, or simply just reading a web board or email message.Usually the attacker will encode the malicious portion of the link to the site in HEX (or other encoding methods) so the request is less suspicious looking to the user when clicked on.For example the code below is written in hex: <ahref=[removed]alert('XSS')>Click Here</a>is equivalent to:<a href=[removed]alert('XSS')>Click Here</a>Note: In the format “&#xhhhh“, hhhh is the code point in hexadecimal form.
- (Exam Topic 3)
What are two functionalities of SDN Northbound APIs? (Choose two.)
Correct Answer:
AB
- (Exam Topic 1)
An engineer is configuring a Cisco ESA and wants to control whether to accept or reject email messages to a recipient address. Which list contains the allowed recipient addresses?
Correct Answer:
D
- (Exam Topic 3)
Refer to the exhibit.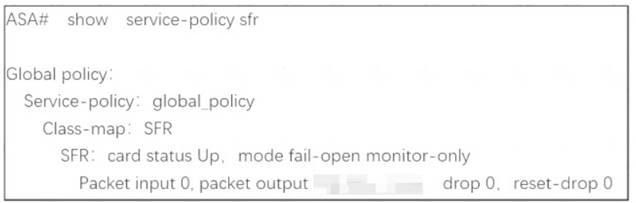
What are two indications of the Cisco Firepower Services Module configuration? (Choose two.)
Correct Answer:
AE
sfr {fail-open | fail-close [monitor-only]} <- There's a couple different options here. The first one is fail-open which means that if the Firepower software module is unavailable, the ASA will continue to forward traffic. fail-close means that if the Firepower module fails, the traffic will stop flowing. While this doesn't seem ideal, there might be a use case for it when securing highly regulated environments. The monitor-only switch can be used with both and basically puts the Firepower services into IDS-mode only. This might be useful for initial testing or setup.

