Scenario: A Citrix Architect needs to assess an existing NetScaler multi-site deployment. The deployment is using Global Server Load Balancing (GSLB) configured in a parent-child configuration. Click the Exhibit button to view the diagram of the current GSLB configuration and parent-child relationships, as well as the status of the sites and the connectivity between them.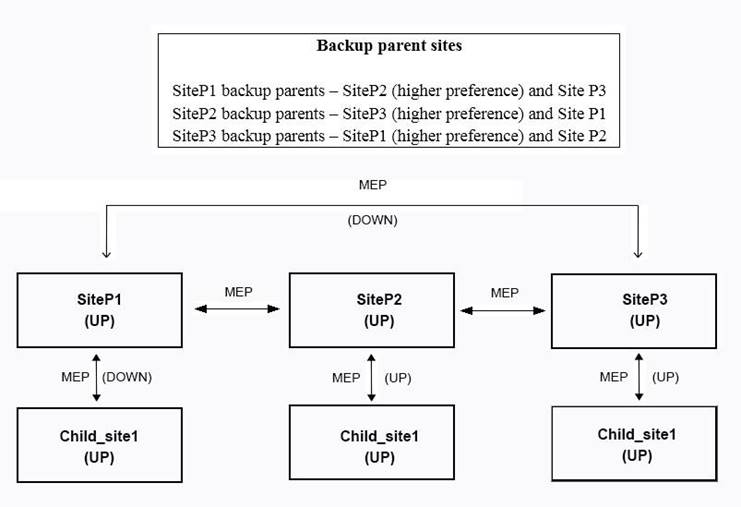
Based on the displayed configuration and status, Chil_site1_____ a connection from ______. (Choose the correct option to complete the sentence.)
Correct Answer:
E
Scenario: A Citrix Architect has set up NetScaler MPX devices in high availability mode with version 12.0. 53.13 nc. These are placed behind a Cisco ASA 5505 Firewall is configured to block traffic using access control lists. The network address translation (NAT) is also performed on the firewall.
The following requirements were captured by the architect during the discussion held as part of the NetScaler security implementation project with the customer’s security team: The NetScaler device:
* Should monitor the rate of traffic either on a specific virtual entity or on the device. It should be able to mitigate the attacks from a hostile client sending a flood of requests. The NetScaler device should be able to stop the HTTP, TCP, and DNS based requests.
* Needs to protect backend servers from overloading.
* Needs to queue all the incoming requests on the virtual server level instead of the service level.
* Should provide access to resources on the basis of priority.
* Should provide protection against well-known Windows exploits, virus-infected personal computers, centrally managed automated botnets, compromised webservers, known spammers/hackers, and phishing proxies.
* Should provide flexibility to enforce the desired level of security check inspections for the requests originating from a specific geolocation database.
* Should block the traffic based on a pre-determined header length, URL length, and cookie length. The device should ensure that characters such as a single straight quote (*); backslash(), and semicolon (;) are either blocked, transformed, or dropped while being sent to the backend server.
Which two security features should the architect configure to meet these requirements? (Choose two.)
Correct Answer:
BE
Reference: https://docs.citrix.com/en-us/citrix-adc/12-1/appexpert/appqoe.html https://docs.citrix.com/en-us/citrix-adc/12-1/appexpert/rate-limiting.html
Which parameter indicates the number of current users logged on to the NetScaler gateway?
Correct Answer:
C
Scenario: The Workspacelab team has configured their NetScaler Management and Analytics (NMAS) environment. A Citrix Architect needs to log on to the NMAS to check the settings. Which two authentication methods are supported to meet this requirement? (Choose two.)
Correct Answer:
BC
Reference: https://docs.citrix.com/en-us/netscaler-mas/12/authentication-and-rbac/configuring.html
A Citrix Architect needs to configure advanced features of NetScaler by using StyleBooks as a resource in the Heat service.
What is the correct sequence of tasks to be completed for configuring NetScaler using the Heat stack?
Correct Answer:
D
Reference: https://docs.citrix.com/en-us/netscaler-mas/12/integrating-netscaler-mas-with-openstack-platform/integrating_netscaler_mas_with_openstack_heat_services.html

